Welcome to our comprehensive FAQ page, your one-stop destination for answers to the most common questions about Dependency Track SaaS and Software Health Indicator.
We’ve gathered and organized the most frequent inquiries to ensure that you have quick and easy access to the information you need. So, dive in, explore, and discover all the essential information about Dependency Track SaaS and Software Health Indicator right at your fingertips.
Frequently Asked Questions (FAQ)
Can Dependency Track SaaS handle a very large application portfolio ?
There is no built-in limit to the number of software SBOMs that can be scanned. At this stage our database can follow up more than 187'000 software vulnerabilities. It could as well follow up several thousands of applications.
Our license subscriptions have a limit, contact us for personalized offer if you need more.
Can I automate sending the SBOMs ?
Do you provide advanced support, tailored customization or API programming assistance ?
Those are not part of our standard support. We do have the competencies in house and can offer them upon specific project agreement.
Contact us for any special inquiries.
Does your solution offer an API ?
How are my personal data handled ?
How can I keep track of my findings regarding a software vulnerability affecting my software ?
In your Dependency Track, under project, audit software vulnerabilities, you can add a comment, categorise, justify and add details.
All information are kept in audit trail available only in your tenant.
How do I generate the SBOMs of my software ?
How much does Dependency Track SaaS cost ?
We offer different monthly and annual packages according to the number of users and project.
Check our Pricing page.
How often is my portfolio of applications scanned ?
Our smart analysis engine ensures your applications risk scores are refreshed whenever needed, that is every time a new software vulnerability is affecting one of your components.
New published software vulnerabilities are imported at least once every day in your personal and private cloud database. By configuring alerts, you will be notified immediately if one of your components is at risk without even having to log into our solution.
How to enable multi-factor authentication (MFA) ?
- As a user, you can self administer your own account from the page
https://auth.yoursky.blue/realms/<YourTenant>/account/, replacing 'YourTenant' with the tenant name received during onboarding. - Select 'Signing In'
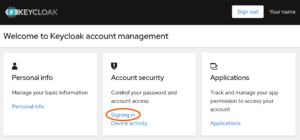
- Then select 'Set up authenticator application' and follow the wizard
As an administrator, you can setup MFA as default policy for every users from the admin console.
How will I discover if I am affected by new software vulnerabilities ?
I am already using an antivirus/malware scanner, why would I need a software vulnerability scanner ?
Antivirus and malware scanners detect malicious codes either at rest or just before execution. An agent needs to be installed on every computer. Such scanners detect the threats only when they are already in the system.
On the other hand, software vulnerability scanners track known weaknesses based on a standardized description of all your software components (SBOM). Monitoring can be performed offline before the system is in production and highlight all potential software vulnerabilities. It serves you to know better your system, focus on prioritized action plan to reach compliance goals, meaning you can invest time and resources where it is most needed to increase your security.
It is frequent that malware exploits known vulnerability. Fixing software vulnerability is closing the door to most malware threats. It is a proactive action that works upstream from antivirus and malware scanners.
Antivirus and software vulnerability scanners provide complementary lines of defense.
I am always updating my components to latest versions, why would I need a software vulnerability scanner ?
Updating software is essential and you should obviously keep doing it. This is, however, insufficient if you are not also keeping track of components which stop receiving regular updates.
Such components that are becoming slowly obsolete or abandoned will put you or your customers at risk. Without using an automated tool, people can barely keep track of first level components and will lack most of the deeply nested ones.
Our solution points out every components, including the deepest ones, which present security risks. The time and energy saved can then be invested more effectively to respond to remaining threats.
I have a webapp/website for which each new version completely replaces the former version. Is there anything different ?
If you fully control the lifetime of a version and can ensure when it is no longer used across the globe (eg: Facebook website), then tracking all the versions ever published is not suitable. It is a special case for which it would be best to monitor only the current version.
You would select `Cloud - single version mode` during you order for this case.
I support different platforms (iOS, Android, Windows, Linux, ...). Can your indicator track them ?
It is possible to generate SBOM for pretty much any platform and technology you might think of. See our cheat sheet.
Even if you provide the same functionality on each platform, they rely on different software components (libraries) and might suffer from different software vulnerabilities. For this reason you need to generate an SBOM for each platform you compile for.
As each platform is tracked individually and might have different release cycles, we require that you buy a different license for each platform.
What are the benefits of Dependency Track SaaS ?
What are the next steps after purchasing Dependency Track SaaS ?
What are the supported notification platforms ?
Slack, Microsoft Teams, Webhooks, Webex by Cisco are supported notification platforms.
Check the Integration Overview Table.
What does Dependency Track SaaS scan ?
What happen if I don't renew my Software Health Indicator license ?
What happens if I don't send updates of SBOM for new versions?
What is your cancellation policy ?
What kind of organization can benefit from your solution ?
What kind of support options do you offer ?
In our standard offers, we provide support to access the solution and store securely your data. We provide all the infrastructures and stop at the boundary of the software.
In particular, there is no support included to manage your data such as data transfers, data intelligence, data cleansing, security audit, ...
Those can be acquired separately if required, please contact us if you need our experts to assist you for those missions.
What language does Dependency Track SaaS support ?
The UI supports several languages:
- German
- English
- Spanish
- French
- Hindi
- Italian
- Japanese
- Polish
- Portuguese
- Portuguese (Brazil)
- Russian
- Ukrainian
- Chinese
Users can change their language preference in their profile settings.
Our service support is proposed in:
- German
- English
- Spanish
- French
Why choose Dependency Track SaaS ?
Why use a cloud solution instead of the free on premise version ?
Both are using the same version of the open source dependency-track.
With the free version, you have to dedicate your own resources and time.
With our cloud based solution, you get everything included: the solution is available and operational within a few minutes after ordering, configured for highest security standards. We operate the solution for you, take care of testing, upgrades, backups, we scale up when needed, and we provide direct assistance in case of difficulties. Your data is kept secured in a dedicated personal tenant.
As a bonus, you get access to a Keycloak tenant preconfigured so that you can easily enable MFA or integrate with your existing user directory. This is not mandatory but we strongly believe this is an important feature for business who care about security and maintainability.
Finally we are expert of the solution and know how to operate it like no one else.
Why are you Swiss-hosted only ?
Could you offer global presence ?
Do you have plans to pursue specific certifications in the near future ?
How should I count users ?
This should be the number of individuals that are eligible to use the solution during the period.
For example, in a company of 500 people, if only a team of 12 is using the solution, 12 is your number of users for our solution.
Later, if one member leaves the company and another one changes to another team, and you effectively revoke their access without letting anyone new in, you could inform us, and we will reduce the number of users to 10 for your next subscription renewal.
How should I count projects ?
This is the number of project entries in Dependency-Track that have at least one component, including projects flagged as inactive.
For example, if you want to track both version 1 and version 2 of your product, you might create a parent project to group the projects for version 1 and version 2. This would still count as 2 projects since the parent project has no components. Later, if you create an additional project for version 3 and mark version 1 as inactive, this counts as 3 projects. However, if you fully delete version 1 instead, the count returns to 2.
If your product consists of several parts, such as a frontend, backend, and several micro services, it is important to determine the appropriate level for tracking software vulnerabilities. If tracking at a higher level is adequate, you can usecyclonedx-cli merge command to regroup certain SBOMs, and reduce the number of projects required.To count the total number of projects you use, in the projects view, activate the Components column and enable the options Show inactive projects and Show flat project view. You can achieve the same with API endpoint.
We understand that it's a bit inconvenient as Dependency-Track currently lacks sorting on the Components column, but we may offer a better solution in the future.
Can we pay by invoice or in cryptocurrencies ?
We can tailor our payment methods to suit your needs.
Please contact our customer service for detailed guidance on how to proceed with your preferred payment method.
How do I configure the SSO with my enterprise IdP ?
Activating Single Sign-On (SSO) will allow your corporate users to log into Dependency Track SaaS through your corporate Identity Provider (IdP), streamlining the login process and greatly simplifying user management. For more information on the advantages of SSO, check out our detailed article. Your Keycloak instance is already pre-configured to act as an intermediary broker for Dependency Track SaaS, leaving only the delegation to your corporate IdP to be configured.
Please note:
Setting up SSO requires coordinated configurations in both your corporate IdP and Keycloak to establish mutual trust. The configuration steps for your IdP will vary depending on the platform you are using (e.g., Entra ID, Okta, Google Workspace, etc.). We recommend consulting your IdP's documentation for detailed instructions, which typically involve creating a client or application profile.
- Access the Keycloak Admin Console: Navigate to
https://auth.yoursky.blue/admin/<YourTenant>/console/, replacingYourTenantwith the tenant name you received during the onboarding process. - Add Identity Provider: Open
Identity Providers, select your identity provider, and fill in all required information. Ensure this matches the client/application profile you created in your corporate IdP. - Test the Configuration: Attempt to log in to your Dependency Track SaaS instance to verify the setup.
- Tune Permissions: Adjust group and mapping settings as necessary to align with your access control requirements.
If you have additional security requirements, such as multi-factor authentication (MFA), ensure these are configured in your IdP for an added layer of protection.
What’s the difference between VDR and VEX, and how should we use them?
VDR (Vulnerability Disclosure Report) and VEX (Vulnerability Exploitability eXchange) are both tools designed to improve software transparency in the era of SBOMs — but they serve different purposes and are often confused.
VDR is a positive disclosure: it lists all known vulnerabilities that do affect a product or its dependencies, along with impact analysis and remediation plans. It is often updated as new vulnerabilities are discovered.
VEX is a negative advisory: it states which vulnerabilities do not affect a product, even if the vulnerable component is present. It helps reduce false positives by clarifying exploitability status.
Both are supported in Dependency Track SaaS and can be used together. VDR gives consumers transparency about known risks, while VEX provides clarity about irrelevant or mitigated ones.
Recommendation:
Use VDR for vulnerability visibility and VEX to eliminate unnecessary concern. Combining both improves trust, accuracy, and efficiency in software supply chain risk management.

Let us know if there is anything else we can assist you with !
Contact us
When can we expect to see content on your social media accounts ?
We are currently working on developing our social media strategy and content plan, and we plan to start posting content soon. We understand the importance of being active on social media and engaging with our audience, so we will be sharing updates on our progress on our website and other channels.
We encourage you to follow our social media accounts now to stay up to date with our progress and be the first to know when we start posting content. You can always contact us or use our social media accounts to reach out to us with any questions or feedback.